ESG reporting has crossed the threshold from voluntary disclosure to mandatory compliance infrastructure. The organisations that treated sustainability reporting as a communications exercise — a curated narrative published once a year in a PDF — are now facing regulatory frameworks that require auditable, granular, continuously collected data across every tier of their supply chains. The question is no longer whether to report, or even what to report. The question is whether the data infrastructure exists to support reporting at the scale and specificity that regulators now require.
The Framework Landscape
The ESG regulatory landscape is simultaneously the most mature and the most fragmented compliance domain in enterprise risk management. Multiple frameworks with overlapping but non-identical requirements apply to the same organisations, and the mandatory versus voluntary status of each framework varies by jurisdiction, sector, and company size. Understanding the landscape is a prerequisite to automating it.
| Framework | Jurisdiction | Status | Key Requirement | Supply Chain Scope |
|---|---|---|---|---|
| CSRD / ESRS | European Union | Mandatory | Double materiality — financial and impact perspectives required | Full value chain Scope 3 disclosure |
| SEC Climate Rules | United States | Mandatory | Climate-related risks and GHG emissions for public companies | Scope 3 for material upstream/downstream |
| GRI Standards | Global | Voluntary | Stakeholder-facing impact reporting across E, S, and G pillars | Significant suppliers and contractors |
| TCFD | Global / UK Mandatory | Mixed | Climate risk governance, strategy, metrics, and targets | Scope 3 categories relevant to climate risk |
| ISO 14064 | Global | Voluntary | GHG quantification, monitoring, reporting, and verification | Organisational boundary definition required |
| ISSB / IFRS S2 | Global / Adopted by 20+ jurisdictions | Emerging Mandatory | Investor-focused climate and sustainability disclosures | Scope 3 where material |
Automating Data Collection
Manual ESG data collection — spreadsheets submitted by suppliers, utility bills reviewed by sustainability teams, carbon factors applied by hand — does not scale beyond a single reporting cycle. It also does not produce auditable data. A spreadsheet submitted by a supplier contains no cryptographic evidence that the numbers are accurate, unmodified, or consistent with the methodology used in the previous period. Automated ESG data collection replaces human data-entry chains with instrumented pipelines that capture data at source, apply consistent methodology, and produce a verifiable record of how every figure in the report was derived.
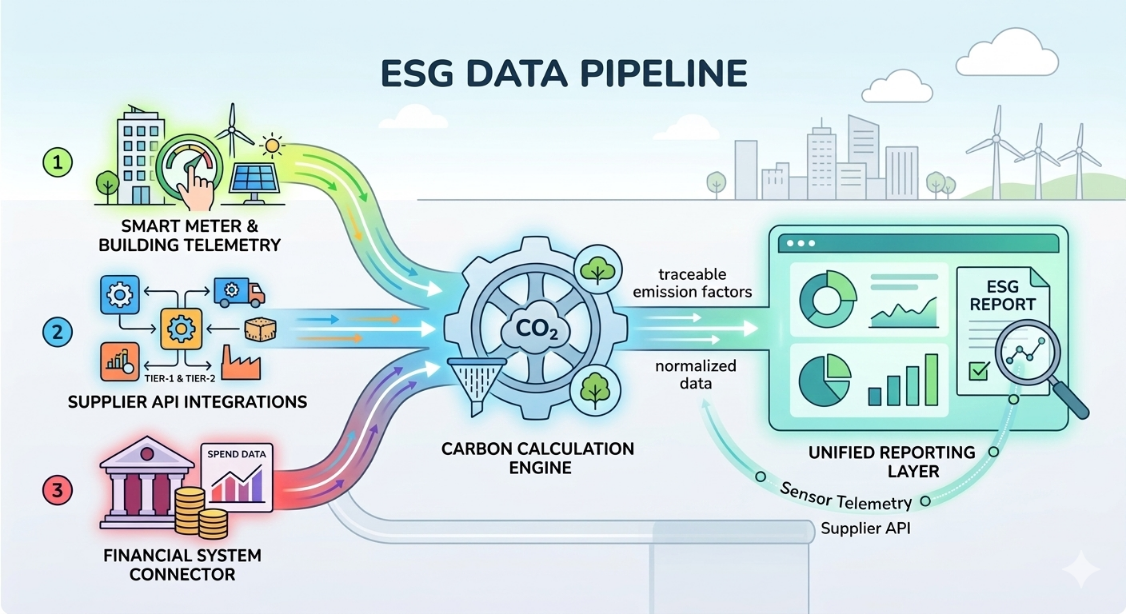
The three primary data sources in an automated ESG pipeline are utility telemetry — smart meter and building management system data feeding directly into emissions calculation engines — supplier API integrations that pull activity data from tier-1 and tier-2 suppliers in real time, and financial system connectors that extract spend data for spend-based Scope 3 estimation where primary activity data is unavailable.
Each source requires a different integration architecture, but all three must feed into a single calculation layer that applies consistent emission factors, handles currency and unit normalisation, and produces output data that is traceable back to its source record for every individual data point in the final report.
Verifiable Data Sovereignty
Verifiable data sovereignty in ESG reporting means that every data point in a compliance report can be traced back to its origin, that the origin data has not been modified in transit, and that the methodology applied to derive the reported figure from the origin data is documented, consistent, and independently verifiable. This is a significantly higher standard than most organisations currently meet — where the provenance of a reported emissions figure often cannot be reconstructed beyond "the sustainability team calculated it."
Supply Chain Compliance at Scale
Scope 3 emissions — those occurring in the value chain outside the direct control of the reporting organisation — represent the majority of most enterprises' total emissions footprint and the most technically complex data collection challenge in ESG compliance. CSRD's full value chain disclosure requirement and the SEC's materiality-based Scope 3 rules both demand that organisations collect, verify, and report data from suppliers who may have no ESG reporting infrastructure of their own.
- Stationary combustion: natural gas, diesel, fuel oil in owned facilities
- Mobile combustion: owned vehicle fleet fuel consumption
- Fugitive emissions: refrigerant leakage, process venting, wastewater treatment
- Process emissions: manufacturing and chemical production sources
- Purchased electricity: grid consumption metered at facility level
- Purchased steam and heat: district energy and industrial heat purchases
- Market-based adjustments: renewable energy certificates, power purchase agreements
- Category 1: Purchased goods and services — supplier primary data or spend-based estimation
- Category 4: Upstream transportation — logistics provider API integrations
- Category 6: Business travel — travel management system connectors
- Category 7: Employee commuting — survey-based or mobility data estimation
- Category 11: Use of sold products — product energy consumption modelling
- Category 12: End-of-life treatment — waste characterisation and disposal route estimation
- Category 15: Investments — financed emissions for financial institutions
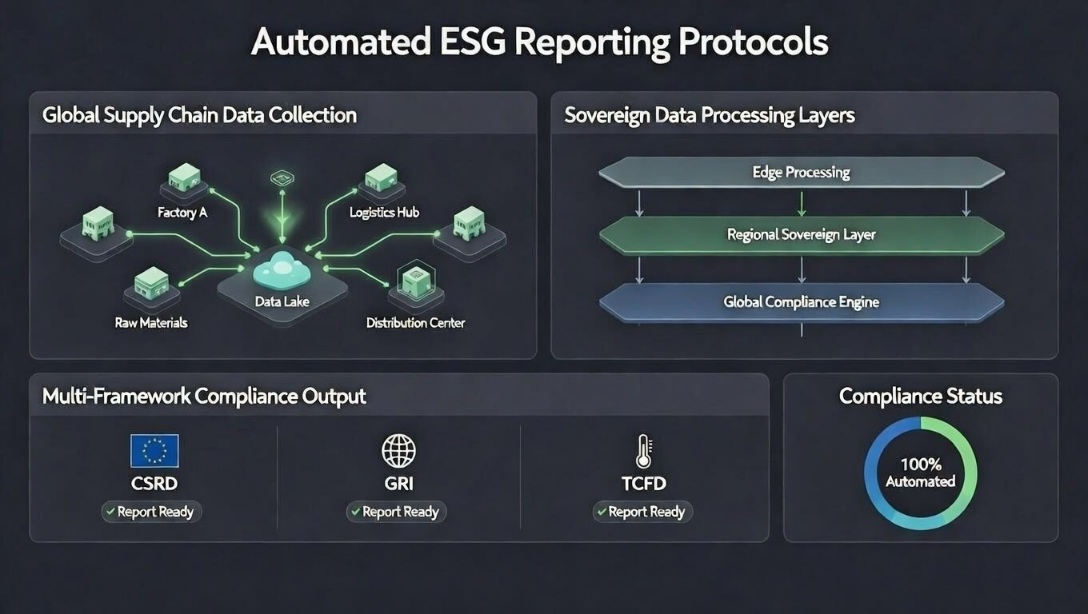
Implementing the Protocol Stack
An automated ESG reporting protocol stack has four layers that must be implemented in sequence. Building the reporting layer before the data collection layer produces reports with no auditable foundation — a common failure mode that creates regulatory exposure rather than reducing it.
- Layer 1 — Data ingestion: Instrumented connections to all primary data sources — utility APIs, fleet telematics, supplier portals, financial systems, and logistics platforms. Each connector must include data quality validation at ingestion to flag missing, anomalous, or inconsistent records before they propagate into calculations.
- Layer 2 — Calculation engine: A documented, versioned calculation layer that applies emission factors, unit conversions, and methodology choices consistently across all reporting periods. The calculation engine must be auditable — every output figure must be traceable to the input data and the calculation logic that produced it.
- Layer 3 — Data sovereignty layer: Cryptographic signing of data at ingestion, immutable storage of raw inputs and calculated outputs, and a chain of custody record that maps every reported figure to its source measurement. This is what transforms ESG data from a set of numbers into auditable evidence.
- Layer 4 — Multi-framework reporting: A reporting layer that maps the calculated, sovereign data to the specific disclosure requirements of each applicable framework — CSRD, GRI, TCFD, ISSB — simultaneously, without requiring manual re-entry or re-calculation for each framework. One dataset, multiple compliant outputs.
Key Takeaways
- ESG reporting has crossed from voluntary disclosure to mandatory compliance infrastructure. CSRD, SEC climate rules, and ISSB adoption across 20+ jurisdictions make automated data collection a regulatory requirement, not a competitive differentiator.
- Manual ESG data collection does not produce auditable data. Provenance cannot be established for figures derived from supplier spreadsheets and manual calculations — which is the standard regulators and auditors now apply.
- Verifiable data sovereignty means a cryptographically intact chain of custody from source measurement to disclosed figure — not just on-premise storage or contractual data handling agreements.
- Scope 3 is where most organisations face their largest data collection gap. Automated supplier API integrations and spend-based estimation engines with documented methodology are the only scalable approaches to full value chain disclosure.
- The protocol stack must be built bottom-up — data ingestion, then calculation, then sovereignty, then reporting. A reporting layer built on unauditable data is a liability, not a solution.